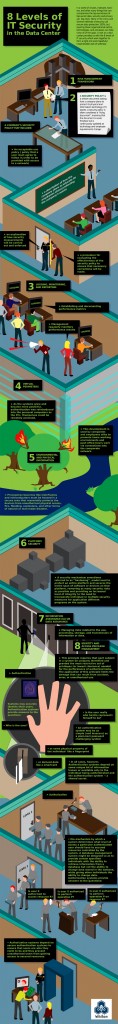
In a world of viruses, malware, and hackers, information security is a big deal. One single method of IT security cannot insure protection of mission-critical data. In the enterprise IT environment, layering multiple tactics and security processes can help close all of the gaps. A visual look at a data center provides us with the 8 levels of information technology security which work together to form a tight-knit and (hopefully) impenetrable web of safeness.