Palo Alto Networks has earned a reputation as the leader in security. You can measure this in revenue, market cap, execution and, most importantly, conversations with CISOs. The company is on track to double its revenues to nearly $7B in FY23 from FY20. This despite macro headwinds which will likely continue through next year. Palo Alto owes its position to a clarity of vision and strong execution of a TAM expansion strategy bolstered by key acquisitions and integrations into its cloud & SaaS offerings.
In this Breaking Analysis, and ahead of Palo Alto Ignite, we bring you the next chapter on top of last week’s cybersecurity update. We’ll dig into the ETR spending data on Palo Alto Networks, provide a glimpse of what to look for at Ignite and posit what Palo Alto needs to do to stay on top of the hill.
The Problem is Clear
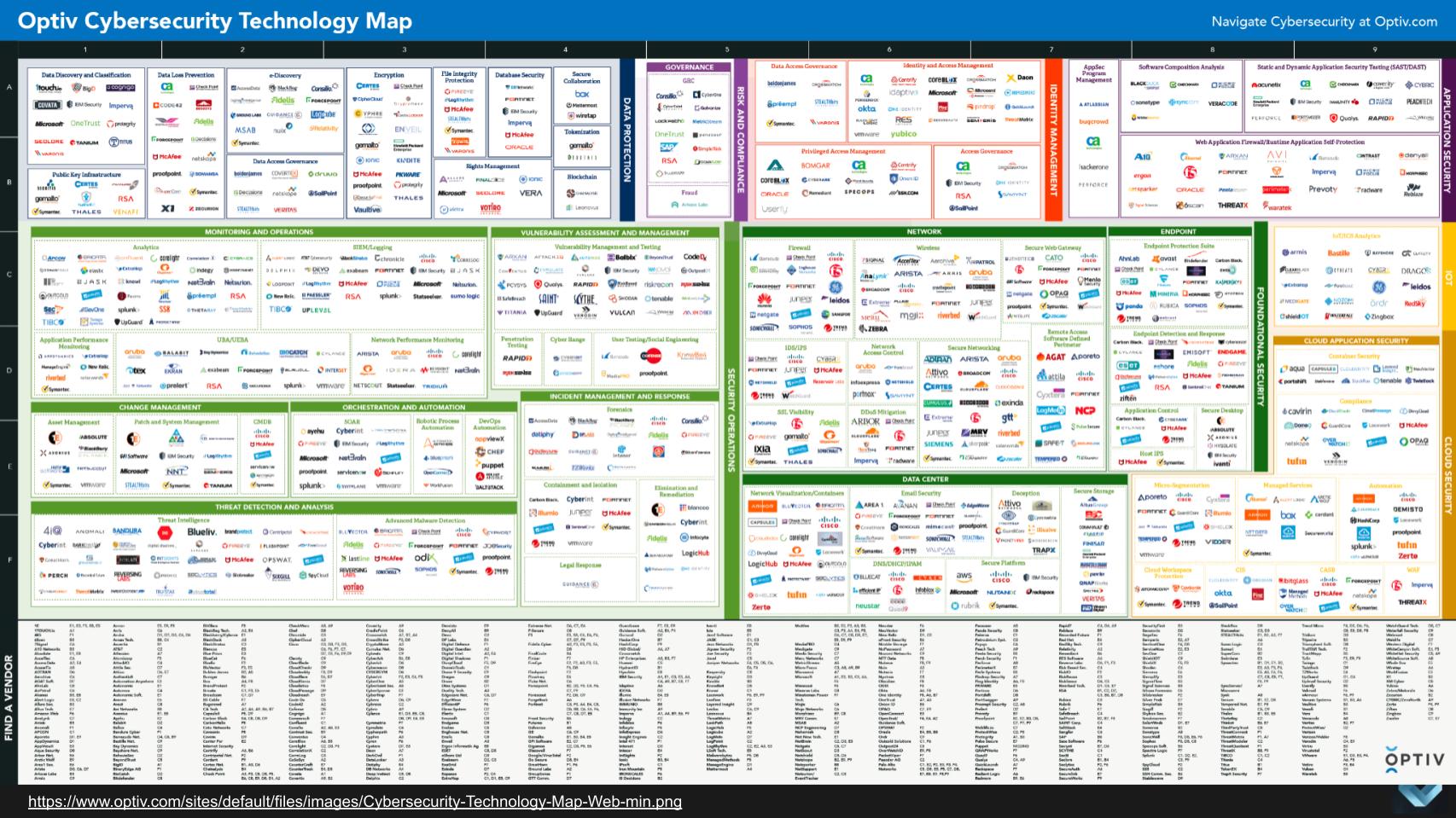
The challenges for cybersecurity professionals is dead simple to understand. Solving it is not so easy.
The taxonomic eye test above from Optiv is one of our favorite artifacts to make the point. The cybersecurity landscape is a mosaic of stovepipes. Security professionals have to work with dozens of tools, many legacy, combined with shiny new toys to try and keep up with the relentless pace of innovation, catalyzed by incredibly capable, well-funded and motivated adversaries.
Cybersecurity is an anomalous market in that the leaders have low single digit market shares. Think about that. Cisco at one point held 60% market share in networking and it’s still deep into the 40s. Oracle captures around 30% of database market revenue. EMC at its peak had more than 30% of the storage market. Dell’s unit PC market share is in the high 20’s. From a market share standpoint, cybersecurity is even more fragmented than the software market.
The point is, despite its position as the #1 player, Palo Alto has maybe 3-4% of the total security market. Depending on your denominator. Regardless, the leader has only a tiny slice.
Why is Palo Alto Considered the Leader?
This CISO’s comments from a recent ETR roundtable discussion with our friend Erik Bradley sums up Palo Alto’s allure pretty well in our opinion.
Why Palo Alto Networks?
Because of its completeness as a platform. Its ability to integrate with its own products…or they acquire, integrate, then rebrand them as their own. We’d looked at other vendors…we just didn’t think they were as mature. We had already implemented some of the Palo Alto tools, the firewalls and stuff. We thought why not go holistically with a vendor, a single throat to choke if you will if stuff goes wrong. And I think that that was probably the primary driver and familiarity with the tools and the resources that they provided.
-CISO in a recent ETR roundtable
The Push to Consolidate Redundant Vendors
Here’s another stat from ETR’s Erik Bradley. He gave us a glimpse of the January survey. The percent of IT buyers stating they plan to consolidate redundant vendors went from 34% in the October survey and now stands at 44%. So we feel this bodes well for consolidators like Palo Alto Networks. Same for Microsoft’s “good enough” approach. It should also be true for Crowdstrike although last quarter we saw softness in their SMB market; whereas MongoDB actually saw consistent strength from SMB so that’s something we’re watching closely.
Palo Alto’s Stock has Fared Better than its Peers
While all growth stocks have been hit hard over the past year, Palo Alto Networks has held up better than most security players.
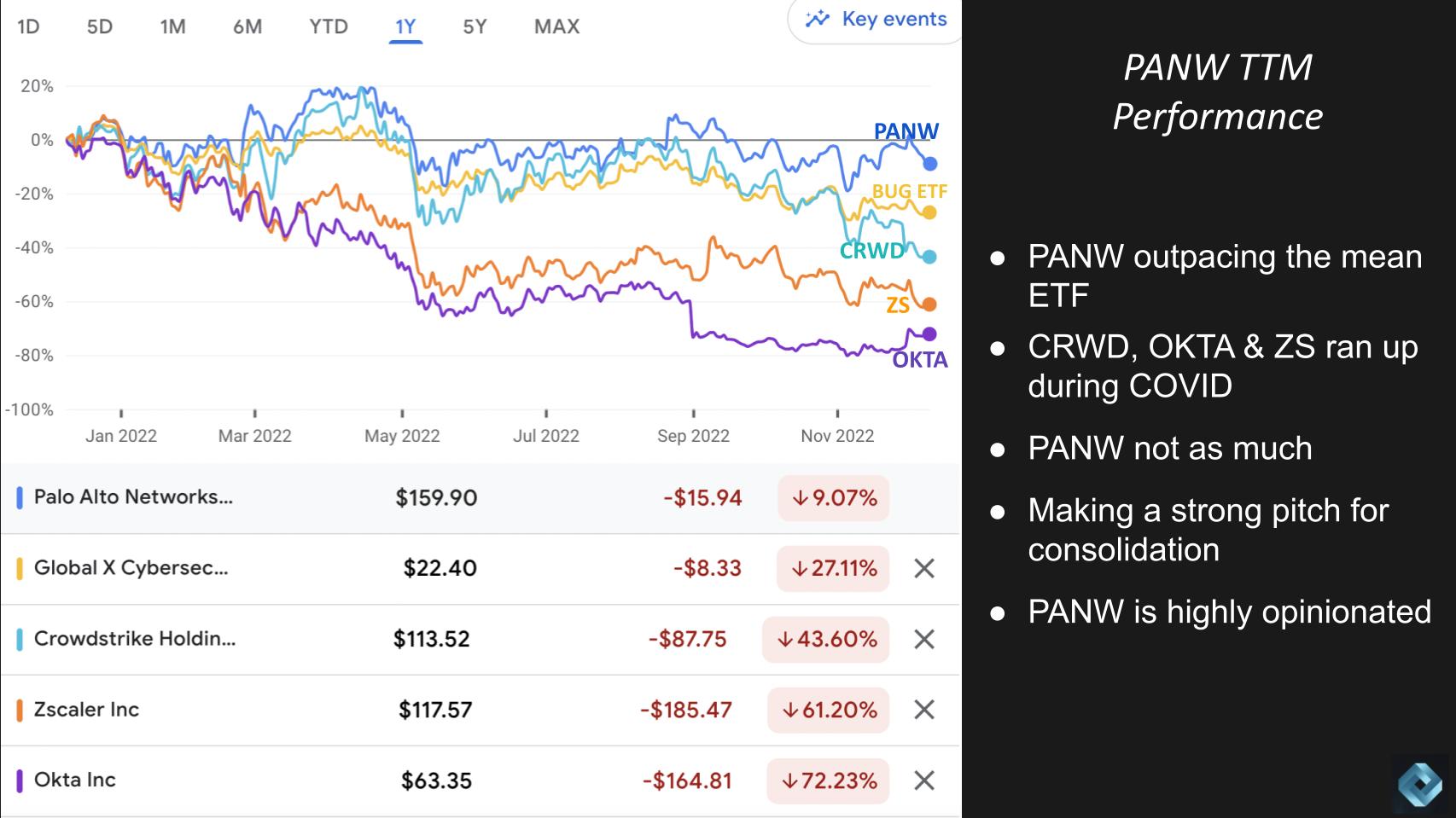
The chart above gives you a sense of how well. It’s a one year comparison of Palo Alto with the BUG ETF, CrowdStrike, Zscaler & Okta. Now remember Palo Alto didn’t run up as much as CROWD, ZS & OKTA during the pandemic, but you can see it’s now down “only” 9% for the year. The cyber basket ETF is off 27%, roughly in line with the Nasdaq (not shown). CrowdStrike down 44%, Zscaler down 61% and Okta off 72% in the last year.
As we’ve indicated, Palo Alto is making a strong case for consolidating point tools. We think it will have a much harder time getting customers to switch off platforms like Cisco, another leader in network security. But based on the fragmentation in the market there’s plenty of room to grow in our view.
How the Traders See it
We asked Breaking Analysis contributor Chip Symington for his take on the technicals of the stock and he said the following:
Despite Palo Alto’s leadership position, fundamentals don’t seem to make much difference these days. It’s all about interest rates. Even though this name has performed better than its peers, it looks like this stock wants to keep testing its 52 week lows.
But he thinks the Palo Alto got oversold during the last big selloff and the fact that the company’s free cash flow is so strong probably keeps it at the 150 level or above. If it breaks that to the downside its next test is around the 140 level according to Symington.
Palo Alto’s Opinionated Point of View
As we said earlier, Palo Alto has strong convictions. Its founder and CTO, Nir Zuk is extremely clear on his view of the market and sets the tone for the company’s strategy. Below we take a look at how Palo Alto got to where it is today and how we should think about its future.
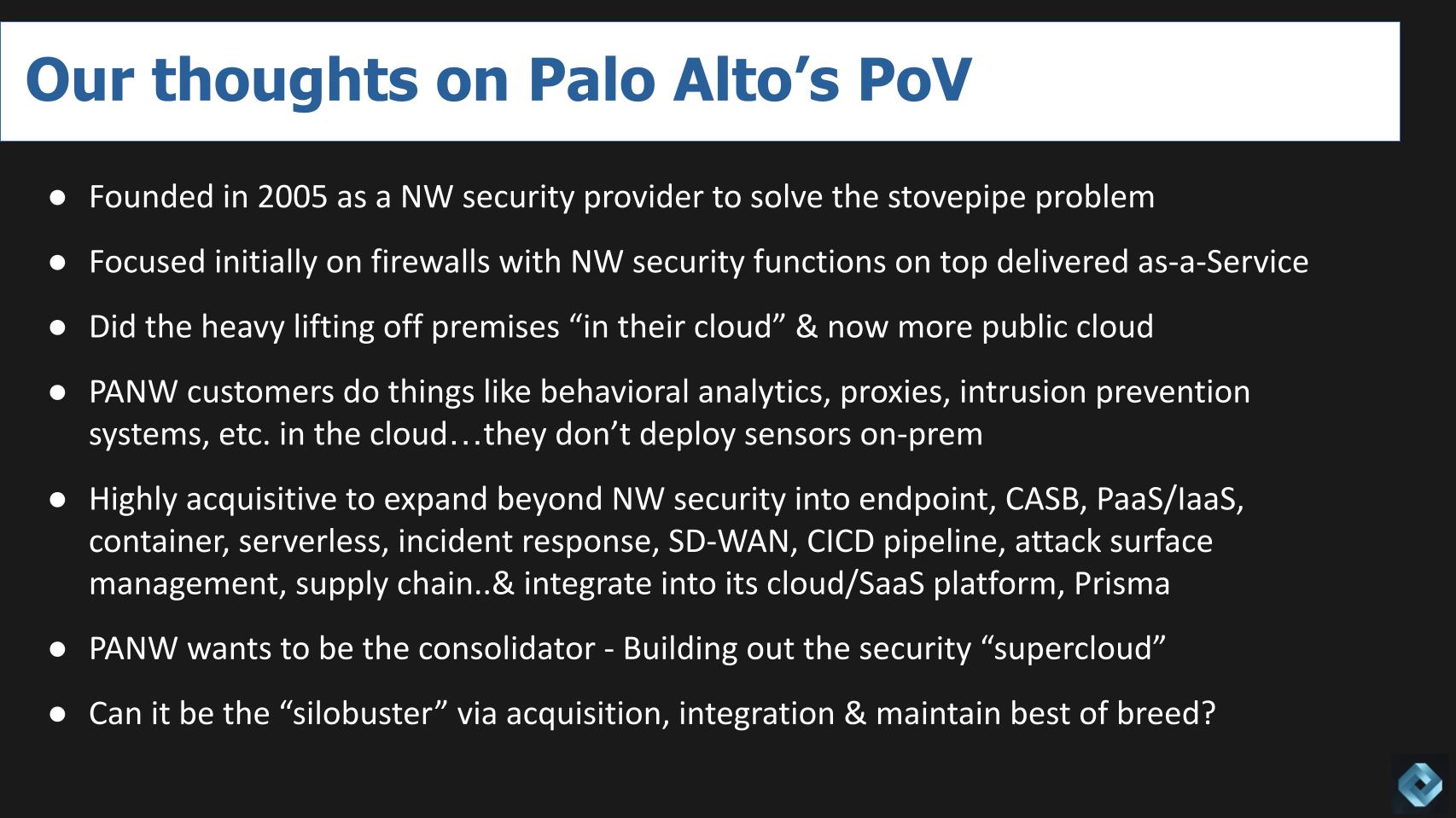
The company was founded around 18 years ago as a network security company focused on firewalls. What Palo Alto did was different. It didn’t try to stuff too much functionality inside of a box. Rather it layered network security functions on top of its firewalls and delivered value as a service through software – running at the time in its own cloud and now heavily leaning into public clouds. A pretty obvious move today but forward thinking for the time.
Palo Alto has invested in building a true cloud native platform. In February 2020, right before the pandemic we reported on the divergence in market values between Palo Alto and Fortinet and cited some challenges Palo Alto had transitioning to a cloud native model. At the time we said we were confident that Palo Alto would make it through the knot hole and you can see from the previous stock chart it has do so.
The company’s architectural approach was to do the heavy lifting in the cloud. This eliminates the need for customers to deploy sensors or proxies on prem. Same with sandboxes on prem which can be vulnerable to overwhelming attacks. Think about it. If your sandbox is on prem it’s not getting updated every day no way. Or even every week. Perhaps even longer. And if the capacity of your sandbox is 20,000 files per hour…a hacker will just overwhelm you by sending 100,000 email attachments so your sandbox will choke and they’ll have the run of the house while you’re figuring out what happened.
The cloud won’t completely prevent this problem but it definitely increases the hackers’ cost so they’ll probably hit easier targets. ROI is the simple algorithm for hackers. ROI = Benefit / Cost. Increase the denominator and ROI decreases, making you a less attractive target.
TAM Expansion Via Acquisitions
The next thing that Palo Alto did is start acquiring aggressively. We counted 17 or 18 acquisitions to increase the company’s total available market beyond network security. Endpoint, CASB, PaaS/IaaS, container, serverless, incident response, SD-WAN security, CICD pipeline security, attack surface management, supply chain security recently, with the acquisition of Cider Security.
Palo Alto by all accounts takes the time to integrate these acquisitions into its cloud/SaaS platform called Prisma. Unlike many acquisitive companies – EMC was a good example where you ended up with a “Franken-Portfolio.”
Palo Alto – Building the Security Supercloud
Consolidation of redundant vendors is the #1 customer cost optimization strategy today. Forty-four percent of ETR survey respondents are actively pursuing this strategy. This leads us to believe that Palo Alto wants to be the consolidator and is in a good position to do so.
But beyond that. As multi cloud becomes more prevalent, customers tell us they want a consistent experience across clouds. This will be the same with IoT. Customers don’t want another stovepipe for edge security. So we think Palo Alto is in a position to build what we call the security supercloud. A layer above the clouds that brings a common experience for devs and operational teams.
Can Palo Alto Remain Best of Breed?
The obvious question for a company rapidly expanding through acquisition is can it continue to effectively integrate new capabilities and still maintain best of breed status? Does it even have to? As Constellation Research analyst Holger Mueller talks about all the time on theCUBE, integrated suites will always beat BoB in the long run if the suite vendor can incorporate important features quickly. Maintaining best-of-breed inside of a suite would be a “game over” strategy.
Palo Alto’s Portfolio is Impressive
This next graphic underscores the point.
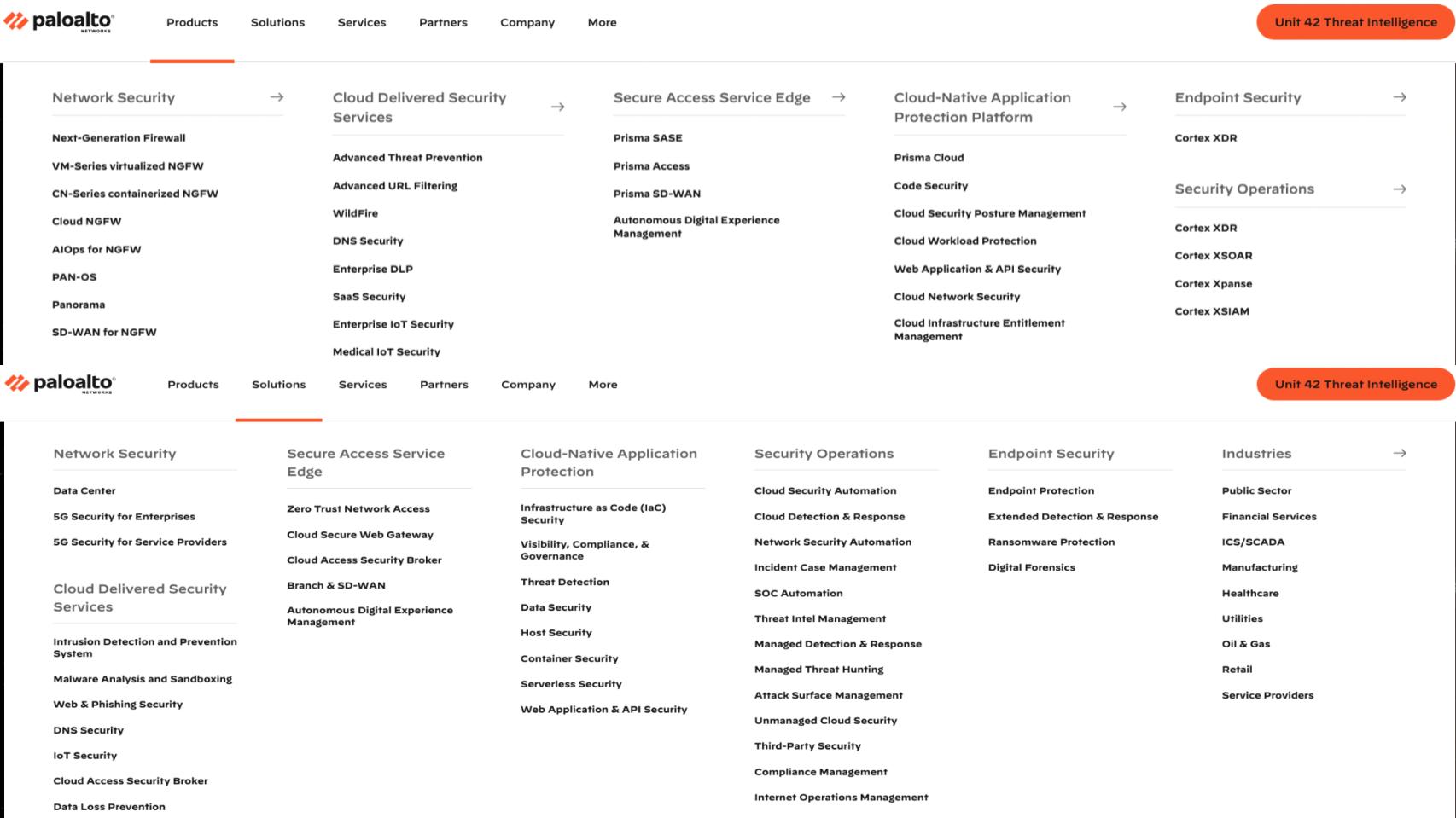
Above is a picture we don’t expect you to fully digest, but it’s a screen grab of Palo Alto’s product and solutions portfolio. Security in areas including network, cloud, SASE, CNAAP, endpoint, Unit 42 (its threat intelligence platform) and every imaginable security service for customers. Well not every…we’re sure there’s more to come like supply chain with the recent Cider acquisition and maybe more IoT beyond Zingbox. But we’re sure there will be more in the future both organic and inorganic.
Palo Alto’s Customer Spending Profile – Very Little Churn
Let’s come back to the ETR spending data.
For those that don’t know ETR, they’re the #1 enterprise data platform surveying thousands of end customers every quarter with additional drill down surveys and customer roundtable. It’s just an awesome SaaS-enabled platform and they’re an amazing contributor to theCUBE.
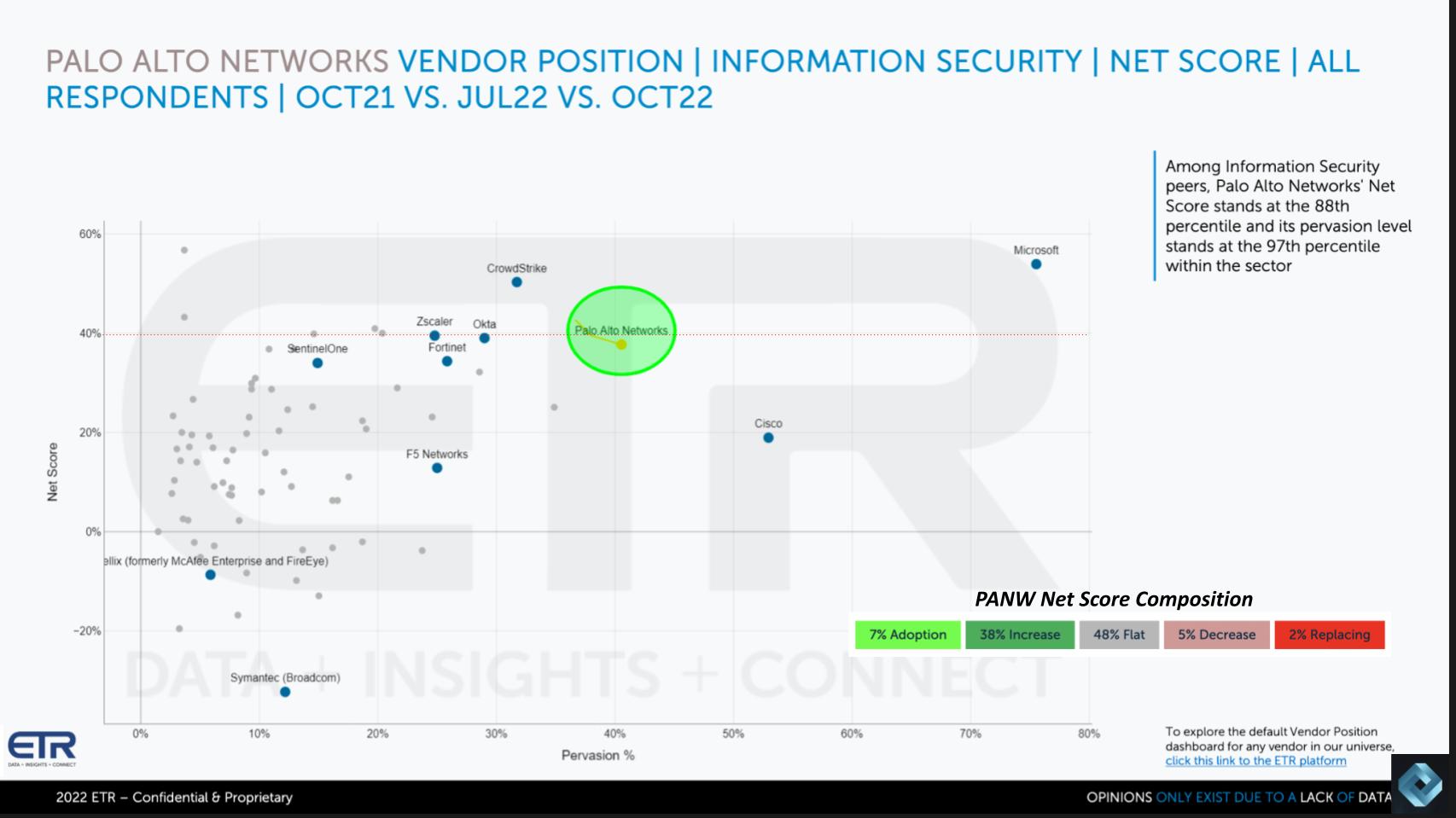
Above is a view that shows Net Score or spending momentum on the vertical axis and Pervasion or presence within the data on the horizontal axis. The red line at 40% indicates a highly elevated Net Score and you can see Palo Alto is right on that line. We’ll give another glimpse of the future survey. It looks like despite the macro, Palo Alto may edge back up in the next survey based on the preview Erik Bradley gave us.
The colored bars in the bottom right corner show the breakdown of Palo Alto’s Net Score. It shows the percent of customers spending in each category. The lime green is new customer adoptions at 7%; the forest green at 38% is the percent of customers spending spending 6% or more, the gray at 48% is spending flat, the pinkish at 5% is spending is down on Palo Alto products by 6% or worse; and the bright red at only 2% is churn or defections.
Subtract the red from green and you get a Net Score of 38%, which is very good for a company of Palo Alto’s size. And we’ll note this is based on nearly 400 respondents that are Palo Alto customers out of around 1,300 in the total survey.
You can see the other leading companies like CrowdStrike, Okta, Zscaler, Fortinet Cisco loom large. Many of those firms have aspirations similar to Palo Alto Networks vis a vis consolidating multiple tools. Including the ever-ubiquitous Microsoft.
Palo Alto Continues to Increase its Market Penetration
Drilling deeper into the ETR data, let’s look at how Palo Alto has progressed over the last three surveys in terms of presence in the ETR survey.
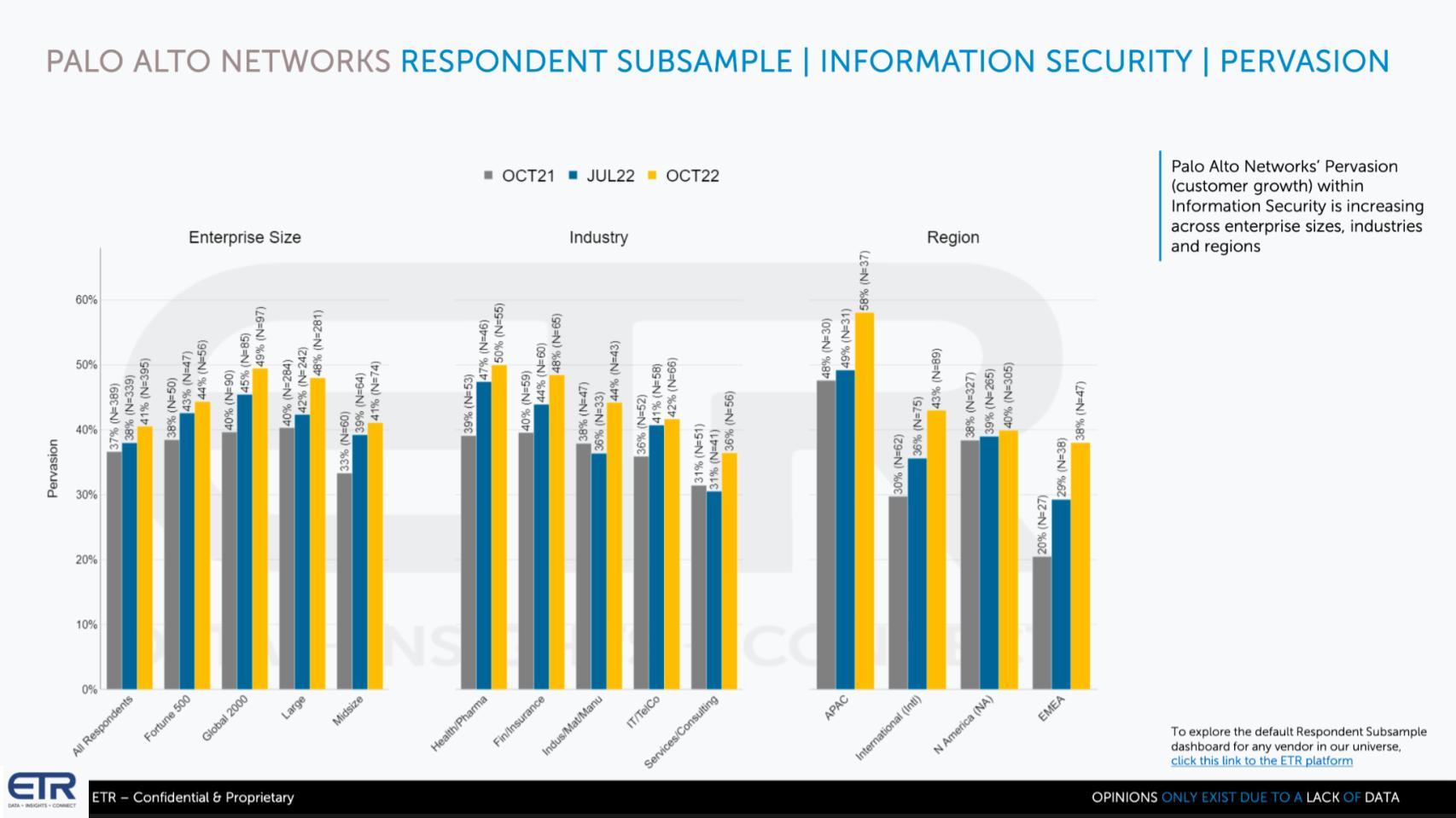
This view of the data above shows Pervasion or presence in the data going back to the October 2021 survey – that’s the gray bars. The blue is July 22 and the yellow is the latest survey form October 2022. Remember January is currently in the field.
The leftmost set show size of company the middle set shows industry and the rightmost shows geographic region. Notice anything? Yes – Palo Alto gaining across the board relative to both this past summer and last fall. So that is pretty impressive.
Palo Alto Networks’ CEO Nikesh Arora stressed on the last earnings call, like other firms, the company is seeing somewhat elongated deal approvals and sometimes splitting up size of deals. He stressed that certain industries like energy, government and financial services continue to spend. But we would expect even a pullback in those sectors as companies get more conservative.
But the point is that Arora stressed the company is aggressively hiring sales pros and taking action to work the pipeline harder. Because they understand they must pull deals forward, get more approvals and increase volume to account for certain companies splitting up deal sizes.
Ignite Preview & The Key to Palo Alto Staying on Top
We’re going to wrap by sharing what we expect and what we’re going to probe for at Palo Alto Ignite next week.
First it’s a four day event at the MGM with the meat of the program on days 2 and 3 when we’ll be broadcasting. Our understanding is it’s a pretty technically oriented crowd that will be eager to hear what CTO and founder Nir Zuk has to say. As well we’ll be speaking to CEO Nikesh Arora, longtime friend of theCUBE and current President BJ Jenkins, Wendy Whitmore, who runs Unit 42 and several other high profile Palo Alto execs.
Thomas Kurian from Google Cloud will also be speaking at the event.
Lee Klarich, who is Palo Alto’s CPO, we think will be giving the audience a heavy dose of Prisma Cloud and Cortex enhancements. Cortex came from an acquisition and does threat detection, attack surface management and security automation. So we’ll be listening for how that’s being integrated and what kind of uptake it’s getting.
One of the other things we’ll be watching is pricing. We’ll be talking to customers about their spend optimization patterns and vendor consolidation strategies. Palo Alto is a premium offering. It charges for value. It’s considered expensive. So what kind of switching costs are customers willing to absorb and how onerous are they? What’s the business case for paying that premium?
And as we discussed earlier, how will Palo Alto maintain best-of-breed feature status as it acquires and integrates? And does it even need to do so?
The Tension Between Regulation & Security
There’s also an interesting dynanic going on in security. A CUBE alum named Edward Haletky is a security pro who has educated us on many aspects of cybersecurity. One area of particular interest he’s talked about are the challenges of securing data and applications while at the same time protecting data privacy. This is especially difficult as public policy evolves, how regulations vary by region and how complicated it is to show a chain of custody that proves unequivocally that data has been deleted. Or that scrubbed data or metadata doesn’t include any residual private data that violates local laws.
The tension is this. You need good data to have good security. The more data the better really. But government policy is often a major blocker to sharing data and it’s getting more restrictive. So we want to understand this tension and how companies like Palo Alto are dealing with it. Are customers testing public policy in courts? Are governments making exceptions in policies like GDPR that favor security over data privacy? What are the tradeoffs there and how are they being managed?
What Keeps Palo Alto on Top?
Finally. One theme of this Breaking Analysis is – what does Palo Alto have to do to stay on top? And we would sum it up with three words – ecosystem, ecosystem, ecosystem. We said at CrowdStrike Fal.con that the one concern we had was the pace of ecosystem development. How inclusive is Palo Alto’s ecosystem. Will Palo Alto collaborate with possible competitors? Is Palo Alto’s portfolio being adopted aggressively by global system integrators and developers? Where do the cloud players fit in the ecosystem? Are they aggressively leaning in to partner or cautiously dancing?
The hallmark of a cloud company, which Palo Alto is a cloud security company, is a thriving ecosystem that has entries into and exits from its platform. So we’ll be looking at what that ecosystem looks like, how vibrant and inclusive it is, where the public clouds fit and whether Palo Alto Networks can really become the security supercloud.
If you’re at Ignite next week, please stop by theCUBE and say hello. If not, as always we always appreciate your candid feedback.
Keep in Touch
Thanks to Chip Symington and Erik Bradley for their contributions this week. Alex Myerson and Ken Shiffman are on production, podcasts and media workflows for Breaking Analysis. Special thanks to Kristen Martin and Cheryl Knight who help us keep our community informed and get the word out. And to Rob Hof, our EiC at SiliconANGLE.
Remember we publish each week on Wikibon and SiliconANGLE. These episodes are all available as podcasts wherever you listen.
Email david.vellante@siliconangle.com | DM @dvellante on Twitter | Comment on our LinkedIn posts.
Also, check out this ETR Tutorial we created, which explains the spending methodology in more detail.
Watch the full video analysis:
Note: ETR is a separate company from Wikibon and SiliconANGLE. If you would like to cite or republish any of the company’s data, or inquire about its services, please contact ETR at legal@etr.ai.
All statements made regarding companies or securities are strictly beliefs, points of view and opinions held by SiliconANGLE Media, Enterprise Technology Research, other guests on theCUBE and guest writers. Such statements are not recommendations by these individuals to buy, sell or hold any security. The content presented does not constitute investment advice and should not be used as the basis for any investment decision. You and only you are responsible for your investment decisions.
Disclosure: Many of the companies cited in Breaking Analysis are sponsors of theCUBE and/or clients of Wikibon. None of these firms or other companies have any editorial control over or advanced viewing of what’s published in Breaking Analysis.